How Cyber Attacks Are Evolving: A Deep Dive into the New Threat Landscape
From automated social engineering to AI-driven exploitation, here is how the digital battlefield is shifting.
The era of static, predictable cyber threats is officially over. Attackers are now deploying autonomous systems that learn, adapt, and strike with unprecedented precision.
Understanding how cyber attacks are evolving is no longer an IT concern; it is a critical necessity for every organization navigating today's complex digital economy.
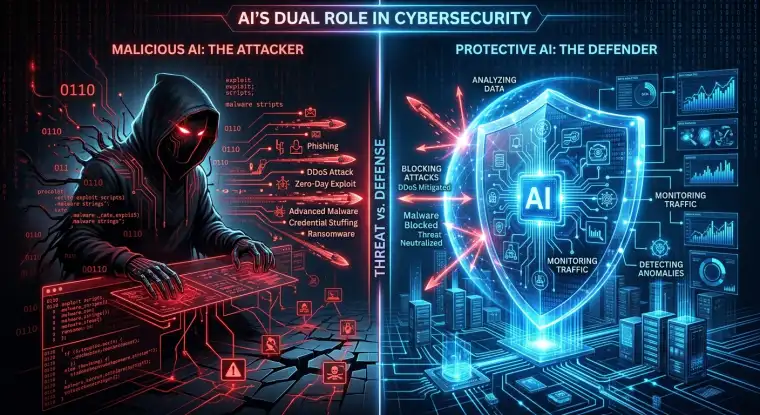
Artificial intelligence is the double-edged sword of our time, simultaneously supercharging defense mechanisms and providing bad actors with sophisticated new weaponry.
In the rapidly transforming world of financial technology, the speed at which systems are adopted is often matched by the speed at which they are targeted. As businesses migrate their infrastructure to the cloud and integrate machine learning into their operations, cybercriminals are following suit, using the same advanced technologies to identify vulnerabilities that were once considered invisible. This evolution signifies a fundamental shift from brute-force attempts to surgical, AI-powered infiltration strategies.
Quick navigation
The rise of AI-powered orchestration
How exactly does machine learning change the nature of a cyber attack? Historically, hackers relied on static scripts and manual exploitation. Today, autonomous agents can perform reconnaissance on a network, identifying open ports or outdated software configurations in real-time without triggering standard security alarms. This automation allows attackers to operate at a scale previously unimaginable, targeting thousands of businesses simultaneously with tailored payloads designed to exploit specific, localized weaknesses.
Furthermore, AI-driven malware is becoming increasingly self-aware. If an attack is detected, modern malicious software can modify its own code to evade signature-based detection systems. By constantly mutating, these threats remain dormant or active for weeks, moving laterally through corporate networks while avoiding traditional perimeter defenses. Is your current security stack prepared to handle software that learns and adapts to your specific internal protocols?
Automated social engineering and deepfakes
Perhaps the most disturbing trend is the evolution of social engineering. In the past, phishing was easily identifiable through poor grammar and generic requests. Now, Large Language Models (LLMs) allow attackers to generate highly convincing, personalized emails that mirror the tone and context of actual colleagues. When combined with synthetic media—deepfake audio and video—attackers can impersonate high-level executives to authorize fraudulent wire transfers or bypass multi-factor authentication.
This personalization makes identifying a threat significantly more difficult. In many cases, the "attacker" is a perfectly tuned algorithm that knows exactly when to reach out to a target to maximize the likelihood of success. Employees must now learn that their digital interactions may be simulations designed to extract sensitive information. Ensuring your team is prepared for such sophisticated deception is critical, much like navigating the digital campus of modern learning institutions requires constant vigilance.
What this means for you
For the average organization, this evolution means that perimeter security is no longer sufficient. If your strategy relies solely on firewalls and basic antivirus software, you are likely already lagging behind. The reality is that attackers will eventually find a way in; therefore, the focus must shift toward resilience and rapid incident response.
How do you plan to detect a breach that appears to be authorized by your own CEO? This is the core challenge of modern cybersecurity. It requires a shift toward a Zero Trust architecture, where no user or device is trusted by default, regardless of whether they are inside or outside the corporate perimeter. Furthermore, legal and operational frameworks must be updated to address these risks. Businesses must demystify the complexities of modern cyber threats to create clear, actionable security policies that every team member understands.
The defense side: Fighting fire with fire
It is not all doom and gloom. The same AI tools being used to attack are also transforming the defensive landscape. Modern Security Operations Centers (SOCs) are now using AI-powered Security Information and Event Management (SIEM) systems to analyze terabytes of network data in milliseconds. These systems establish a baseline of "normal" activity and alert human analysts the moment a subtle anomaly is detected, often stopping an attack before it reaches the payload stage.
By leveraging predictive analytics, companies can now anticipate where an attack might originate based on global threat intelligence feeds. This proactive approach turns security from a reactive cost center into a strategic asset. However, relying entirely on AI for defense brings its own set of challenges, particularly the danger of algorithmic bias or false positives, which can paralyze operations if not properly tuned by human experts.
Risks, trade-offs, and blind spots
The arms race between offensive AI and defensive AI comes with significant trade-offs. The most prominent risk is the "complexity trap," where organizations implement so many security tools that the system becomes unmanageable. When a breach occurs, the sheer volume of data produced by these tools can make it impossible for human responders to determine the root cause quickly.
Another major blind spot is the reliance on third-party vendors. As companies outsource more of their infrastructure, they inadvertently expand their attack surface. If a single software provider is compromised, their AI-enabled tools could potentially be used to distribute malware downstream to all their clients. How much control do you have over the security posture of your cloud service providers? This question should be at the forefront of every digital strategy.
Main points
- Cyber attacks are shifting from manual, brute-force efforts to autonomous, AI-driven campaigns.
- AI-powered malware can mutate in real-time, making it significantly harder for traditional antivirus software to detect.
- Social engineering has been weaponized by LLMs and deepfakes, making phishing attempts nearly indistinguishable from legitimate communications.
- Zero Trust architecture is now a foundational requirement for any robust security strategy.
- The defensive side is also evolving, with AI providing the speed and analytical power needed to combat modern threats in real-time.
- Over-reliance on complex security tools can create operational blind spots and slow down incident response.
- Continuous human oversight is non-negotiable; AI should assist, not replace, security professionals.
The digital threat landscape is volatile, but staying informed is your first line of defense. Assess your current infrastructure today and contact our security consultancy team to schedule a comprehensive vulnerability audit.