Demystifying YIKES: A Guide to the Cybersecurity Acronym
Understanding the Essentials in the Digital World
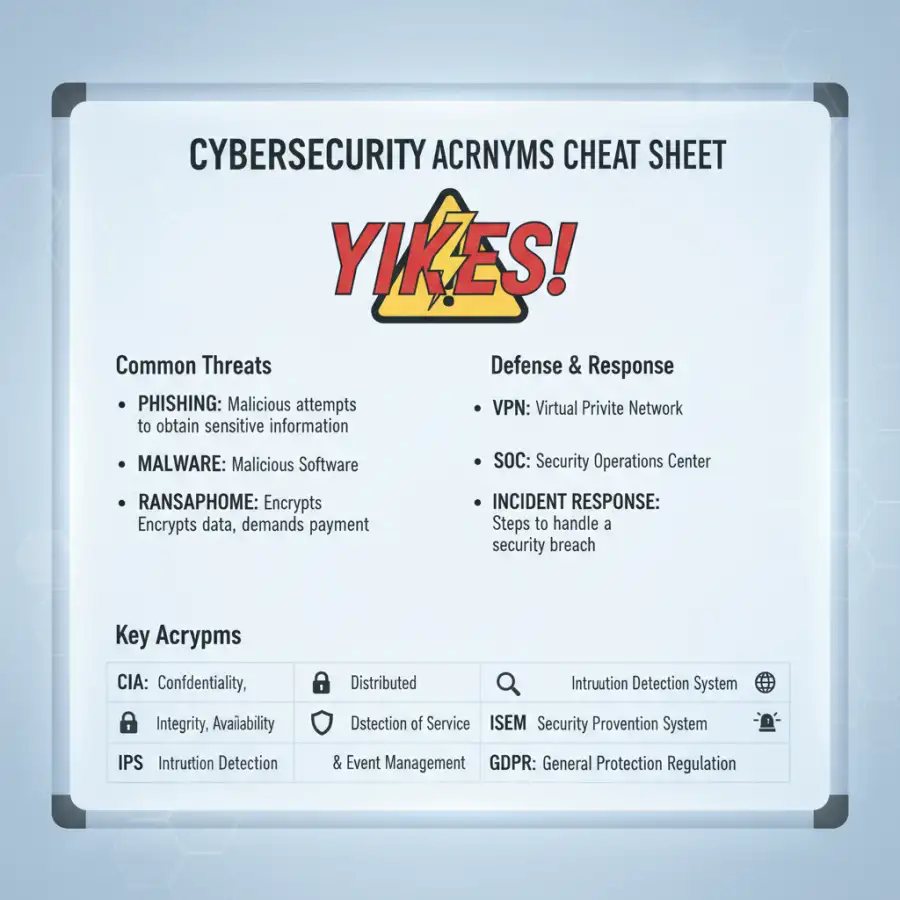
Cybersecurity has complex language and many acronyms. What does it all mean for you?
One acronym is gaining popularity: YIKES. It is more than an expression of surprise. It helps you understand modern digital threats.
This guide will break down the YIKES acronym. You will learn to navigate the cybersecurity field with confidence.
Staying informed about the latest threats and terminology is important in digital security. You will see the acronym "YIKES." This guide explains what YIKES means in cybersecurity, its importance, and why you should understand it. We will also cover topics like phishing, incident response, the 5 C's, and the 7 domains of cybersecurity.
Quick navigation
- What Does YIKES Stand For?
- The Significance of YIKES in Cybersecurity
- Understanding Phishing and Its Connection to YIKES
- Incident Response: The Action Plan When YIKES Happens
- The 5 C's of Cybersecurity
- The 7 Domains of Cybersecurity
- What this means for you
- Risks, trade-offs, and blind spots
- Main points
What Does YIKES Stand For?
The YIKES acronym in cybersecurity represents elements that often come with security breaches or vulnerabilities. It is not a formal standard, but it is a helpful memory aid. It is often used to quickly communicate aspects of a security issue. The exact meaning of YIKES can change slightly depending on the context, but it includes these core areas:
Y - Your systems are vulnerable: A security flaw or weakness exists in your digital infrastructure.
I - Immediate impact: You need to pay attention to this situation and take action.
K - Knowledge of the attack: You now know about the nature of the threat or breach.
E - Exposure of sensitive data: Data breaches may have happened, or sensitive information has been compromised.
S - Security measures need to be improved: You need to reassess and improve your security protocols.
Understanding what YIKES means is the first step in preparing for a digital security threat. Awareness of the different parts of the acronym allows for a more focused and effective response.
The Significance of YIKES in Cybersecurity
Why should you care about YIKES? It is a quick way to assess a situation's severity and understand potential damage. When you hear "YIKES" in security, something is seriously wrong and needs quick action. The acronym helps teams and people understand the severity of a cyber incident. It is a quick way to summarize a complex event.
YIKES reminds you that cybersecurity is not just about the right tools. It is also about understanding and responding to incidents effectively. The acronym helps you categorize and contextualize the situation so you can take proper security measures. The faster you understand the situation, the faster you can respond.
Is understanding YIKES enough to protect you? No, but it is an important first step.
Understanding Phishing and Its Connection to YIKES
Phishing is a common attack method that often triggers a YIKES moment. It involves attempts to get sensitive information, such as usernames, passwords, and credit card details, by pretending to be trustworthy. Phishing attacks can lead to data breaches. They are a significant threat to cybersecurity.
How does phishing relate to YIKES? Phishing is a primary method for attackers to exploit vulnerabilities, leading to system compromises. When a phishing attack succeeds, it can lead to:
- Vulnerability: The attacker gets into your system.
- Immediate Impact: Your system is compromised.
- Knowledge: The attacker knows your login credentials.
- Exposure: Sensitive data can be accessed.
- Security Improvement Needed: Your system security is weak, and new protocols are needed.
Recognizing and defending against phishing is essential to reducing YIKES moments.
Incident Response: The Action Plan When YIKES Happens
Incident response includes procedures to find, contain, and recover from a security incident. A well-defined incident response plan is important when a YIKES scenario happens. This plan should include these steps:
- Identification: Finding and confirming the security incident.
- Containment: Limiting the impact of the incident.
- Eradication: Removing the cause of the incident.
- Recovery: Restoring systems and data.
- Lessons Learned: Analyzing the incident to prevent future occurrences.
Does your organization have an incident response plan? Create one now if you do not!
The 5 C's of Cybersecurity
The 5 C's give a framework for a strong cybersecurity strategy. They are principles that, when followed, help defend against cyber threats. The 5 C's include:
- Compliance: Following laws, regulations, and standards.
- Controls: Using security measures to protect assets.
- Culture: Promoting a security-focused environment.
- Communication: Clearly explaining security policies and procedures.
- Continuous Improvement: Regularly reviewing and updating security measures.
Following these 5 C's can reduce the chance of a YIKES situation.
The 7 Domains of Cybersecurity
The 7 domains offer a comprehensive approach to cybersecurity. They cover all aspects of an organization's digital assets. These domains include:
- User Domain: Focuses on user education, awareness, and training.
- Workstation Domain: Securing endpoints like laptops and desktops.
- LAN Domain: Securing the local area network.
- WAN Domain: Securing the wide area network.
- Remote Access Domain: Securing access for remote users.
- System/Application Domain: Protecting applications and systems.
- Data Domain: Protecting sensitive data.
Do you know how well your organization addresses the 7 domains of cybersecurity? Are there weaknesses?
What this means for you
Understanding YIKES and related concepts gives you an advantage in the digital world. It helps you assess threats quickly. You understand their impact and take action. This knowledge is not only for cybersecurity professionals. It is valuable for anyone who uses the internet.
By learning about YIKES, phishing, incident response, the 5 C's, and the 7 domains, you can better protect yourself, your family, and your organization from cyber threats.
Risks, trade-offs, and blind spots
Understanding these cybersecurity concepts is important. There are risks, trade-offs, and potential blind spots you need to know about. You cannot always prevent every attack. Cybercriminals are always adapting. It is important to stay updated.
Some potential risks and trade-offs include:
- Constant vigilance: You need to learn continuously to stay informed about threats.
- Resource allocation: Implementing strong security can be expensive and take time.
- False sense of security: Relying too much on tools or processes can create blind spots.
Remember, the goal is not to eliminate all risk but to manage it effectively.
Main points
This guide explained the YIKES acronym in cybersecurity and its importance, along with essential concepts. Here is a recap:
- YIKES is a memory aid used to quickly assess the severity of a cybersecurity incident.
- Understanding YIKES involves recognizing vulnerabilities, assessing impact, acknowledging the attacker's knowledge, understanding data exposure, and improving security measures.
- Phishing is a common attack method that often leads to a YIKES situation.
- Incident response plans are important for managing and reducing the impact of security incidents.
- The 5 C's (Compliance, Controls, Culture, Communication, Continuous Improvement) give a framework for a strong cybersecurity strategy.
- The 7 domains (User, Workstation, LAN, WAN, Remote Access, System/Application, Data) offer a comprehensive approach to cybersecurity.
- Cybersecurity awareness is vital for both individuals and organizations.
- Ongoing education and adaptation are essential for staying ahead of evolving cyber threats.
You are on your way to navigating the complex world of cybersecurity with greater confidence. Stay alert, stay informed, and always be prepared. For more information, check out Navigating Digital Campus – Your Ultimate Guide or learn about Online School Programs: College Your Way.

