I Switched to Zero Trust: A Comprehensive Guide
Understanding and Implementing Zero Trust Security
Are your digital defenses truly secure?
Trusting by default is risky.
This guide shows you how to apply Zero Trust to protect your digital environment.
Switching to a Zero Trust security model changes how organizations approach cybersecurity. This method moves away from trusting users and devices inside the network. Zero Trust always verifies. Every user, device, and application must be checked before getting access to resources. This approach is important in today's digital world. The attack surface is always growing. Understanding Zero Trust and how to use it is key to improving your security.
This guide explains the main ideas of Zero Trust. It gives you a clear understanding of its parts, benefits, and how to use this security framework. We will look at the main parts of Zero Trust, its advantages, potential problems, and steps for a smooth transition to a Zero Trust environment.
Quick navigation
What is Zero Trust?
Zero Trust is a security framework. It does not trust anything, including users, devices, and networks. It requires checking every access request. This makes sure every user and device is verified before accessing resources. This model does not automatically trust any user or device. This idea came from the need to fix the problems with older security models. These models often fail to account for new threats like insider threats, stolen credentials, and advanced persistent threats (APTs).
The main idea is "trust nothing, verify everything." This ensures every access request is checked. This includes identity verification, device checks, and continuous authorization. Zero Trust is not a specific product or technology. It is a way to design and plan to secure all digital interactions.
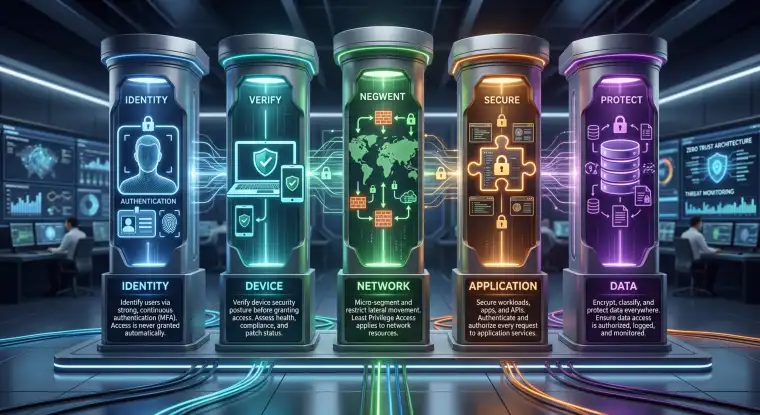
The Five Pillars of Zero Trust
Zero Trust uses main principles or pillars to guide its use. These pillars help organizations build a strong Zero Trust system. The CISA (Cybersecurity and Infrastructure Security Agency) highlights five key pillars. These pillars are important for a strong security system. What are these elements, and how do they work?
The CISA's five pillars include:
- Identity: Check and manage the identities of users and devices. Make sure they are who they say they are. Use multi-factor authentication (MFA), strong passwords, and continuous identity verification.
- Devices: Make sure all devices connecting to the network meet security rules. This includes device checks, endpoint detection and response (EDR), and regular updates.
- Network: Separate the network to limit movement. Use micro-segmentation to limit access to only necessary resources. Use network monitoring and intrusion detection systems.
- Applications: Secure applications by checking their security, using the least privilege principle, and using application-level security controls. Use strong access controls and regular security assessments.
- Data: Protect sensitive data with encryption, data loss prevention (DLP), and access controls. Data classification and monitoring keep data secure, no matter where it is.
How Does Zero Trust Work?
Zero Trust uses policies and technologies. These constantly check the identity, context, and security of every user and device before allowing access. This process is different from older security models. Older models often give broad network access based on location, not identity. What are the key elements that make this possible?
Here is how it works:
- Authentication: Users and devices must verify their identity. They often use multi-factor authentication (MFA).
- Authorization: Once authenticated, access is granted based on the least privilege principle. Users only access the resources they need.
- Context-Aware Access: Access is decided based on factors like device security, location, time, and user behavior.
- Micro-segmentation: The network is divided into smaller, separate zones. This limits movement if a breach occurs.
- Continuous Monitoring and Validation: Security systems constantly monitor and validate user activity and device health. They detect and respond to threats in real-time.
Benefits of Zero Trust Security
Using a Zero Trust security model can improve an organization's security and reduce its exposure to cyber threats. How can Zero Trust improve an organization's security and efficiency?
- Reduced Attack Surface: Limiting access to only needed resources makes it harder for attackers to compromise systems.
- Improved Threat Detection and Response: Constant monitoring and real-time threat detection allow for faster responses to security incidents.
- Enhanced Data Protection: Zero Trust protects sensitive data with encryption, access controls, and data loss prevention.
- Increased Compliance: Zero Trust helps organizations meet compliance requirements by using strong security controls and audit trails.
- Improved User Experience: Zero Trust solutions can improve the user experience. They provide secure access to resources.
Risks, trade-offs, and blind spots
Zero Trust has advantages. It also has potential risks and areas that need attention. What are some possible downsides that organizations should consider?
- Complexity: Using Zero Trust can be complex. It requires planning, resources, and expertise. This is partly because of the need to combine different security tools.
- Cost: The initial investment in Zero Trust technologies and the ongoing costs of maintenance can be high.
- User Experience: Security controls can sometimes affect productivity.
- Compatibility Issues: Integrating Zero Trust solutions with older systems can be difficult.
- Vendor Lock-in: Relying on one vendor can limit flexibility and increase costs.
Real-World Considerations and Implementation
Using a Zero Trust system requires careful planning, execution, and continuous monitoring. What are the key steps in moving to a Zero Trust model?
- Assess Current Security Posture: Check existing security measures and find gaps.
- Define Access Policies: Set clear access policies based on the least privilege principle.
- Implement Multi-Factor Authentication (MFA): Use MFA for all users and devices.
- Segment the Network: Create micro-segments to limit movement.
- Deploy Endpoint Security: Use EDR solutions to monitor and respond to threats.
- Monitor and Analyze: Continuously monitor and analyze user activity and device health.
- Automate Security Processes: Use automation to streamline security operations.
- Provide User Training: Educate users on Zero Trust principles and best practices.
What this means for you
Using Zero Trust security means you are committed to protecting your digital assets. The use of Zero Trust is becoming more important. Are you ready to improve your digital security?
By switching to a Zero Trust framework, you are not just using new technology. You are using a new security approach. This change needs a deep understanding of the risks, rewards, and key elements of Zero Trust. When you use a Zero Trust security model, you improve your security, reduce the attack surface, and protect your data.
Main points
Switching to a Zero Trust security model needs a complete approach. It also needs continuous verification and monitoring. The change from trust to verification is a big step. It is important for organizations that want to improve their cybersecurity. Considering the main points above can help you create a successful strategy.
- Zero Trust uses the principle of "never trust, always verify."
- The five main pillars of Zero Trust are: Identity, Devices, Network, Applications, and Data.
- Zero Trust improves security by reducing the attack surface.
- Continuous monitoring and real-time threat detection are key.
- Implementing a Zero Trust system needs planning and execution.
- Access decisions consider device posture, location, and user behavior.
- Network micro-segmentation limits movement during breaches.
- Zero Trust helps organizations meet compliance requirements.
By understanding the concepts and following the guidelines, organizations can move to a Zero Trust security model. They can better protect their data and assets. If you want to know more, explore Zero Trust with Navigating Digital Campus, learn about FinTech with Wikipedia, and see how to get more of your own license with Licensing Myths Exposed.