This Tool Found Risks I Didn't Expect: A Guide to Uncovering Hidden Vulnerabilities
Uncover the hidden dangers lurking in your projects and systems.
Have you ever deployed a project, only to discover a critical vulnerability you never saw coming?
What if there was a tool that could identify these hidden risks, giving you a clear path to better security and project stability?
This guide explains how these tools work and what you can do to find unexpected vulnerabilities in your code.
Finding and reducing risks is very important in software development. Unexpected problems can quickly ruin a project. They can lead to financial losses and damage your reputation. Tools that find vulnerabilities can be very helpful. This guide explains these tools, their features, and how to understand their findings. It will help you protect your projects and systems from threats.
Quick navigation
Understanding Risk and Vulnerabilities
You must understand risk and vulnerability before using these tools. Risk is the possibility of loss or harm. This could be security breaches, data problems, financial loss, or damage to your reputation. Vulnerabilities are weaknesses that attackers can use. These can come from coding errors, design flaws, wrong settings, or outdated software. What is the difference between a vulnerability and a risk?
Think about a web application with a SQL injection vulnerability. This is the vulnerability. If an attacker uses this, they can access the database without permission. This can cause data breaches or system problems. The risk is the possible damage from using the vulnerability. The more damage possible, the higher the risk.
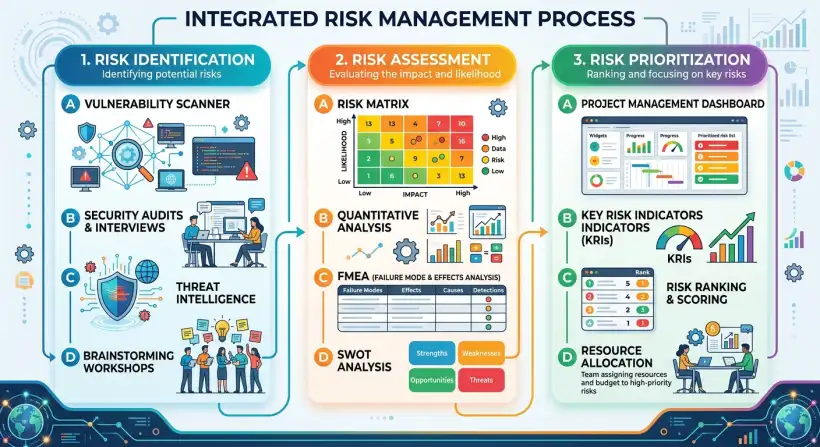
Risk assessment is the process of finding, analyzing, and ranking potential risks. It involves these steps: identifying risks, analyzing risks, ranking risks, and planning how to respond to risks. Identifying risks means finding all possible risks that could affect the project or system. Analyzing risks means assessing the chance and impact of each risk. Ranking risks means putting risks in order based on how likely they are and how much impact they could have. Planning how to respond to risks means creating strategies to reduce, avoid, move, or accept the risks.
Types of Risk Detection Tools
Different tools can help find vulnerabilities and assess risks. Each has its own strengths and weaknesses. SAST tools analyze code for vulnerabilities without running the code. DAST tools test running applications by simulating attacks. SCA tools identify open-source components and check their security risks. What are the key differences between these different types of tools?
SAST tools, also called "white-box testing" tools, examine the code. They can find coding errors, security flaws, and compliance issues early in development. They are good at finding vulnerabilities like buffer overflows, SQL injection flaws, and cross-site scripting (XSS) vulnerabilities. DAST tools, or "black-box testing" tools, simulate attacks against a running application. They do not need the code and can find vulnerabilities that might not be obvious in the code, like configuration issues or runtime errors. DAST tools are often used to test web applications. SCA tools analyze your software's components. They help you find the open-source libraries, frameworks, and other components used in your applications. They check for known vulnerabilities and license compliance issues. They create a software bill of materials (SBOM) that lists all the components used in your software.
Other tools include penetration testing tools, which simulate real-world attacks to find vulnerabilities. There are also vulnerability scanners, which automatically scan systems for known vulnerabilities based on their settings. Each type of tool offers different insights. A good risk assessment strategy often uses multiple tools to get a full view of potential risks.
How Tools Surface Unexpected Findings
Risk detection tools can find unexpected things in several ways. They use techniques like pattern matching, data flow analysis, and taint analysis to find vulnerabilities. Advanced algorithms can detect small flaws that humans might miss. Are you surprised by how these tools can detect vulnerabilities?
Pattern matching means searching the code for known vulnerabilities or coding patterns. Data flow analysis tracks how data moves through the system to find potential security issues, like exposing sensitive data. Taint analysis tracks where data comes from and how it is used. This helps find injection vulnerabilities. For example, a tool might see that user input is used directly in a SQL query without proper checks. This means there could be a SQL injection vulnerability.
Tools also surprise you with how much they analyze. They can examine the entire codebase, including third-party libraries and dependencies. This gives you a complete view of the attack surface. They can also find misconfigurations and other vulnerabilities that might be missed during manual reviews. These tools are updated regularly with new vulnerability signatures and analysis techniques, so they can identify new threats.
False Positives and AI-Specific Risks
Risk detection tools are very helpful, but they also have limitations. One common problem is false positives. This is when the tool flags a possible vulnerability that is not a real risk. This can waste time and resources. How can we reduce false positives?
To reduce false positives, you should adjust the tool's settings and analysis rules to match your project's technologies and coding standards. This helps reduce the number of irrelevant findings. It is also important to check each flagged issue to see if it is a real threat. False negatives, when the tool misses a real vulnerability, are another potential problem. This is why you should use multiple tools and techniques to get a complete view of the potential risks. As artificial intelligence (AI) and machine learning (ML) are being used more in software development, new risks are appearing. For example, AI models can be vulnerable to attacks where people change the input data to make the model give wrong answers. AI systems can also be biased, which can lead to unfair results.
Choosing the Right Tool
Choosing the right risk detection tool depends on factors like the project's size, complexity, technologies, and security needs. For small projects, a SAST tool might be enough. For larger projects with complex systems, you may need a combination of SAST, DAST, and SCA tools. What are the key features to look for in a risk detection tool?
Consider whether the tool can work with your existing development processes. The tool should be easy to use and create clear reports. It should also be able to handle large codebases and complex systems. The tool should offer many features, including support for different programming languages, vulnerability detection, and reporting. The tool should also fit well into your existing development tools and processes. Think about the tool's vendor and community support. A tool with an active community and good vendor support can provide helpful assistance and updates. Finally, consider the tool's cost. Some tools are free, while others are commercial products that cost money. Decide which tool offers the best value based on your budget and needs.
Implementing Risk Detection: A Step-by-Step Guide
To use risk detection tools effectively, follow these steps. First, define your security goals and needs. Then, choose the right tools for your project. Next, set up the tools to scan your code and systems. How do we ensure effective implementation of these tools?
Integrate the tools into your development pipeline so that security checks are automated and done regularly. Analyze the tool's findings and prioritize vulnerabilities. Fix the vulnerabilities by correcting the code, applying patches, or reconfiguring systems. Update the tools regularly with the latest vulnerability information and security best practices. Watch the tool's performance and make adjustments as needed. By following these steps, you can use risk detection tools effectively and improve the security of your projects.
What this means for you
Understanding and using risk detection tools can greatly impact your work. It gives you a way to be proactive about security. You can find and fix vulnerabilities before they can be used. This will help you protect your projects from security breaches and other potential threats. This knowledge can also help you reduce development costs and improve efficiency. How can learning about risk detection tools help your career?
You can improve your skills and advance your career in cybersecurity or software development. Understanding risk detection tools makes you a more valuable part of any project team. You will be better at protecting your organization's data and systems. You will also show that you are committed to security and quality. By learning these tools, you are investing in your future.
Risks, trade-offs, and blind spots
Risk detection tools offer many benefits, but there are also risks and trade-offs. One risk is the possibility of false positives and false negatives, which can waste resources and give you a false sense of security. The time and effort needed to set up, maintain, and understand the tools can be significant. What are the common trade-offs when using these tools?
There is also a trade-off between how thoroughly the tool analyzes and how quickly it scans. More thorough scans may find more vulnerabilities, but they also take longer. You must find the right balance to get the most from the tools. When choosing tools, remember that the tools are only as effective as the developers using them. Problems can happen if developers do not understand the tool's findings or if they do not fix the vulnerabilities correctly. Another trade-off is the cost of using the tools. Some tools are free, while others can be expensive. Consider your budget and your project's needs to choose the right tools.
Main points
- Risk detection tools are essential for finding and reducing vulnerabilities in software projects and systems.
- SAST, DAST, and SCA tools offer different ways to find security flaws. Using a combination of tools often gives the best results.
- Tools can find unexpected things through pattern matching, data flow analysis, and taint analysis.
- False positives and AI-specific risks create challenges that you must address through careful settings and monitoring.
- Choosing the right tool depends on the project's size, complexity, technologies, and security needs.
- Implementing risk detection involves defining security goals, choosing the right tools, setting them up, including them in the development process, analyzing findings, and fixing vulnerabilities.
- Understanding and using these tools can lead to better security, lower development costs, and improved career opportunities.
- Be aware of the risks of false positives and negatives, the time and effort required, and the cost of the tools.
By understanding how these tools work, you can greatly improve your project's security. It is critical to assess vulnerabilities in today's digital world. Take the first step toward a more secure future by exploring and using the right tools for your specific needs.